Cockpit dashboard is a convenient dashboard for home user or enthusiasts for monitoring several SOHO servers. It supports multiple Linux based operating system, however there are some caveats in installing in Raspberry Pi 3 as it runs on older Bookworm based operating system.
first your need to add bookworm-backports.
echo "deb http://deb.debian.org/debian ${VERSION_CODENAME}-backports main" | sudo tee /etc/apt/sources.list.d/backports.listThen you need to configure the keyring
curl -O http://http.us.debian.org/debian/pool/main/d/debian-archive-keyring/debian-archive-keyring_2023.4_all.deb
sudo dpkg -i debian-archive-keyring_2023.4_all.deb Afterwards, you need to run this combo command to update software packages list
apt update && apt -y upgradeThen finally you install cockpit via bookworm-backports
apt install -t bookworm-backports cockpitAfter everything is done, you may check cockpit dashboard by going to:
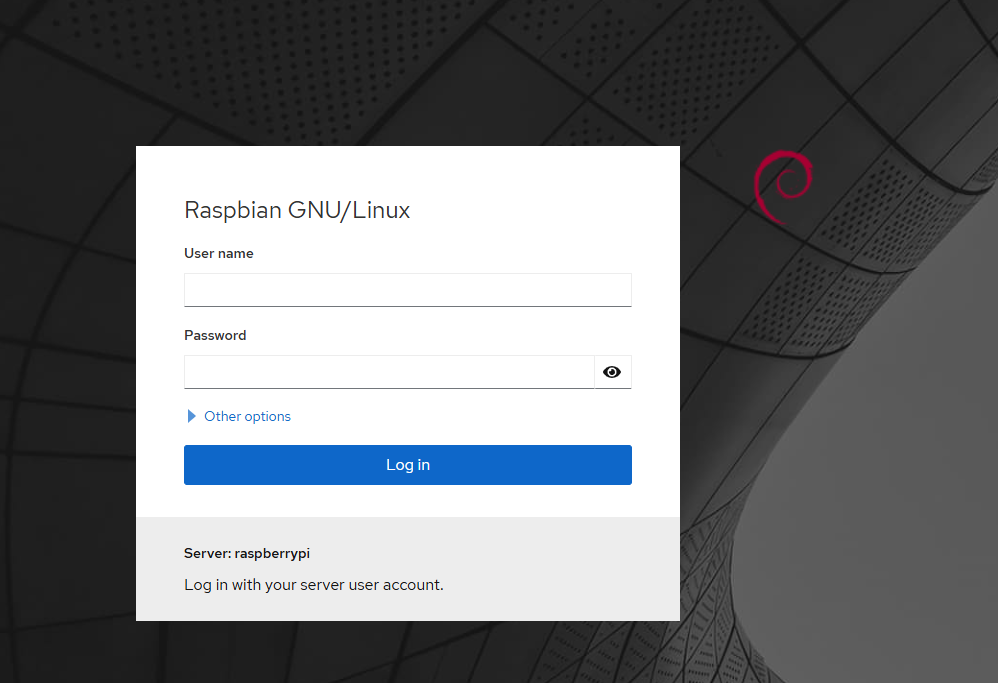
http://<ip address>:9090. and log in using your system username and password.