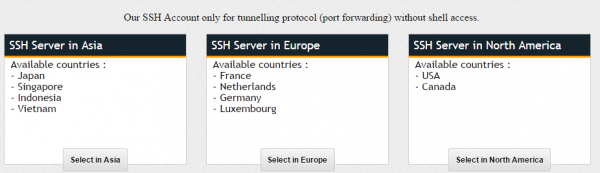
OpenSSH usually listens on TCP port 22. However, there are some people who wish to change OpenSSH port to avoid brute-force bot attacks or to avoid from being blocked by restrictive firewall.
To change OpenSSH port, one only need to edit “/etc/ssh/sshd_config” file and change the port at “Port 22” to something else, like “Port 8080” or “Port 443”
#/etc/ssh/sshd_config # What ports, IPs and protocols we listen for Port 8080
Save, and restart ssh server.
sudo service ssh restart
Additionally you can also configure OpenSSH to listen to multiple port (usually to avoid restrictive firewall rules)
#/etc/ssh/sshd_config # What ports, IPs and protocols we listen for Port 22 Port 8080 Port 443
The example above shows a configuration which lets OpenSSH to listen to port 22, 443 (TLS/SSL) and port 8080 (HTTP-PROXY), these are the ports that usually unblocked by corporate firewall.
Don’t forget to restart ssh service as soon as you’ve save the file!!