Fail2ban is a security tool used for preventing brute-force attack and Distributed Denial of Service (DDoS) attack to your GNU/Linux box.
Fail2ban monitors failed login attempts and subsequently blocks the ip address from further logins. Although Fail2ban can also be used to secure other services in Ubuntu server, in this post, I will only focus on securing SSH server.
Step 1: Install Fail2ban and (optionally) sendmail
sudo apt-get install fail2ban
sudo apt-get install sendmail-bin
Step 2: Setting up Fail2ban
Next, you need to configure fail2ban by creating a copy of ‘jail.conf’ to ‘jail.local’
cd /etc/fail2ban
sudo cp jail.conf jail.local
Step 3: General fail2ban configuration
Edit fail2ban configuration file using your favorite text-edito (I personally use ‘nano’)
sudo nano /etc/jail.local
You can set IP address for fail2ban to ignore, IP addresses can be separated by space.
Bantime is the duration of time that you want fail2ban to block suspicious attempt, the value is in seconds
Maxretry is the number of failed attempts before fail2ban block the IP-address, in this case 3600 means 1-hour ban
# "ignoreip" can be an IP address, a CIDR mask or a DNS host
ignoreip = 127.0.0.1 192.168.1.1
bantime = 3600
maxretry = 3
Step 4: Enabling ssh and ssh-ddos protection
Find ssh configuration under [ssh] heading, and enable it.
[ssh]
enabled = true
port = ssh
filter = sshd
logpath = /var/log/auth.log
maxretry = 3
Similarly, you can also enable [ssh-dos] protection by changing the enabled value to “enabled = true”
[ssh-ddos]
enabled = true
port = ssh
filter = sshd-ddos
logpath = /var/log/auth.log
maxretry = 2
Step 5: Enable Sending Notification Email (optional)
Optionally you can have fail2ban sends you notification email in case of suspicious login detected. To do that, you need to locate destemail settings and changed it to your email
destemail = security@mypapit.net
Fail2ban can use ‘sendmail’ and ‘mail’ application to send notification email
Step 6: (Re-)start Fail2ban
After all is done, you may save the file, and (re)start the fail2ban service
sudo /etc/init.d/fail2ban restart
You can test the configuration by trying to login into your box. You may also check fail2ban log in /var/logs/auth.log (or in other directory specified in jail.local)
For more information about fail2ban, you can read : the official fail2ban manual
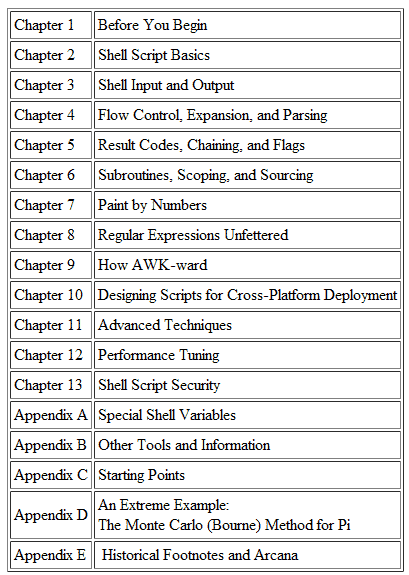
Recommended Reading